Saudi Arabia’s transformation under Vision 2030 is redefining how institutions operate, compete, and protect strategic assets. In this environment, digital infrastructure is a core instrument of institutional sovereignty.
For the Kingdom’s leading healthcare providers and enterprise organizations, security cannot be reactive. It must be engineered into the architectural core. Clinical platforms, AI diagnostics, revenue systems, and cloud environments require infrastructure designed to absorb complexity without exposing critical data or disrupting continuity.
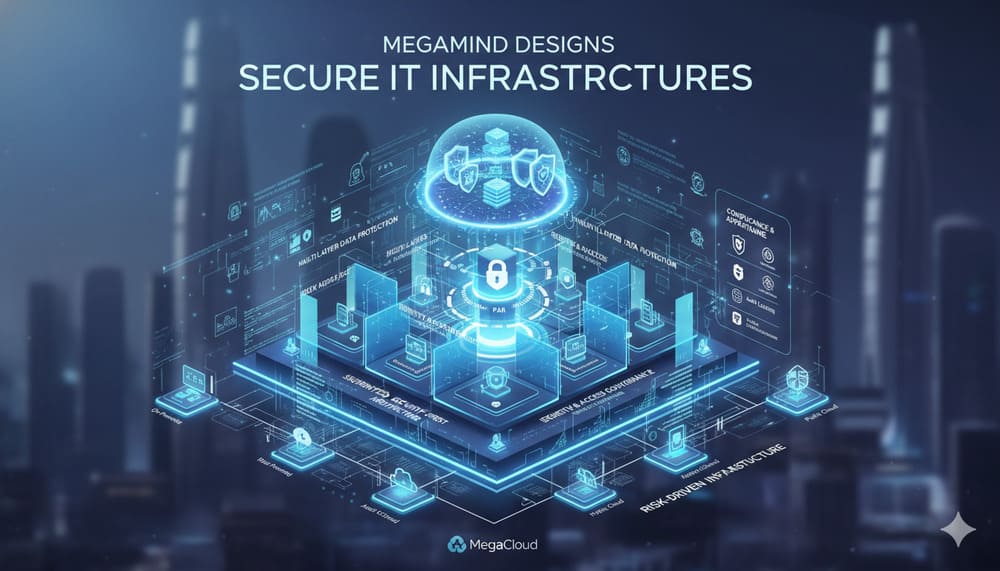
Megamind architects secure IT infrastructures that integrate intelligence-driven defense, regional regulatory alignment, and scalable cloud frameworks. The architecture sustains growth while maintaining strict control over data integrity, system availability, and compliance requirements.
This level of structural control is the result of a deliberate, security-by-design methodology applied at every layer of the environment.
- Establishing a Risk-Driven Infrastructure Foundation
Before deployment, Megamind conducts structured diagnostics across infrastructure layers, application ecosystems, data pathways, and identity environments. The objective is full-spectrum visibility into operational risk.
The foundation is built through:
- Risk mapping across on-premise, hybrid, and cloud environments.
- Critical asset classification and workload prioritization.
- Regulatory gap analysis aligned with Saudi and regional frameworks.
- Business continuity modeling and recovery objective definition.
- Healthcare-specific threat modeling based on current attack vectors.
This risk-driven methodology ensures infrastructure decisions are strategic, measurable, and aligned with business objectives.
- Engineering a Segmented, Security-First Architecture
Without structural segmentation, a single point of compromise can disrupt multiple critical systems.
Megamind engineers architectures that divide infrastructure into controlled security zones, each defined by function, sensitivity, and risk classification. Clinical platforms, financial systems, AI workloads, administrative services, and external-facing applications operate within clearly enforced boundaries.
Segmentation is implemented through:
- Enterprise campus and data center architecture design.
- Software-Defined Networking (SDN) and intent-based policy controls.
- Zero Trust network access enforcement.
- Next-Generation Firewalls and intrusion prevention systems.
- Secure SD-WAN for multi-site healthcare and enterprise environments.
Access between segments is governed by identity validation, strict policy enforcement, and continuous traffic inspection.
This architectural discipline reduces lateral threat propagation, protects high-value systems, and sustains operational continuity across distributed facilities.
- Enforcing Identity, Access & Governance Controls
Identity is the control plane of modern infrastructure.
Megamind implements identity-centered governance models that regulate who can access which systems, under what conditions, and with what level of authority. Every access request is evaluated against role definition, risk posture, and policy enforcement rules.
The governance framework integrates:
- Identity and Access Management (IAM).
- Privileged Access Management (PAM).
- Multi-Factor Authentication (MFA).
- Identity-based Network Access Control (NAC).
- Role-based and least-privilege authorization models.
Access is continuously validated, logged, and adjusted based on user role, device context, and behavioral indicators.
This governance structure constrains privilege escalation, reduces credential-based exposure, and preserves operational continuity across clinical and enterprise environments.
- Architecting Multi-Layered Data Protection & Resilience
In healthcare and regulated enterprise environments, data availability supports operational continuity. Clinical systems, financial platforms, and AI-driven applications depend on infrastructure designed to withstand disruption.
Megamind implements multi-layered protection across endpoints, networks, applications, and storage environments. Controls are applied throughout the data lifecycle, from transmission to archival.
The framework includes:
- Endpoint Detection and Response (EDR).
- Data Loss Prevention (DLP) and classification controls.
- Encryption for data at rest and in transit.
- Web Application Firewalls and secure API gateways.
- Structured backup architecture and Disaster Recovery planning.
Recovery parameters are defined according to service criticality and operational dependency, ensuring prioritized restoration and sustained system integrity across hybrid environments.
- Integrating Real-Time Monitoring & Threat Response
Security architecture depends on continuous visibility. Threat patterns evolve, credentials are compromised, and misconfigurations introduce exposure across distributed environments.
Megamind integrates real-time monitoring capabilities across network, endpoint, and cloud environments to detect anomalies, policy violations, and emerging threats.
The monitoring framework includes:
- Security Information and Event Management (SIEM) platforms.
- Continuous log aggregation and behavioral analytics.
- Vulnerability and patch management programs.
- Advanced threat detection and sandboxing.
- Managed Security Operations Center (SOC) and Network Operations Center (NOC) services.
Incidents are evaluated based on risk severity, system impact, and service criticality. Response protocols are predefined to contain disruption and preserve operational stability across distributed environments.
Compliance Alignment & Operational Assurance
Infrastructure security in healthcare extends beyond technical controls. Regulatory accountability, audit readiness, and data governance are embedded requirements within modern digital environments.
Megamind’s network & digital infrastructure capabilities align infrastructure design with applicable Saudi and regional healthcare regulations, as well as international data protection standards where required. Compliance obligations are translated into architectural controls, access governance policies, audit logging mechanisms, and data handling procedures.
Key elements include:
- Regulatory framework alignment and documentation mapping.
- Secure audit logging and event traceability.
- Data classification and retention policy enforcement.
- Role-based access governance and privilege monitoring.
- Continuous compliance posture assessment.
Continuous control validation preserves regulatory alignment and operational stability across clinical and enterprise systems.
The Business Impact of Security-First Design
Security-first infrastructure shapes operational stability, executive decision-making, and long-term scalability.
When architecture is built on structured risk modeling, segmentation, identity governance, and layered resilience, organizations operate with defined control over exposure. System availability improves. Recovery timelines are predictable. Regulatory oversight becomes manageable rather than disruptive.
For healthcare providers, this translates into sustained clinical continuity, protected patient data, and stable revenue operations. For enterprise leadership, it enables confident cloud expansion, AI adoption, and multi-site growth without structural redesign.
Infrastructure maturity reduces uncertainty in transformation initiatives. Strategic investments move forward within governed boundaries, supported by measurable security controls and operational clarity.
Build a Secure Infrastructure That Scales with Your Business
Strengthen your digital foundation with infrastructure engineered for resilience, governance, and long-term scalability.
Megamind delivers secure IT architectures designed specifically for healthcare and enterprise environments across the Kingdom and the region. Through MegaCloud and its integrated ecosystem, we design, implement, and manage environments that support cloud expansion, AI deployment, regulatory compliance, and multi-site growth without structural compromise.
Our approach combines architectural discipline, intelligence-driven security operations, and regionally aligned governance frameworks to ensure every system operates within controlled, measurable parameters.
Collaborate with Megamind to design secure infrastructure aligned with your growth, compliance, and innovation roadmap.
Read More
- ERP Solutions for Healthcare Organizations in Saudi Arabia
- How to Reduce Hospital Claim Denials by 30% Using Smart RCM
- RPA in Saudi Hospitals: Automate Billing, Scheduling and Claims
- What Is Telemedicine and How Is It Regulated in Saudi Arabia?
- Cloud Computing for Healthcare in Saudi Arabia: Opportunities and Challenges